CVE-2019-11634 DetailCurrent DescriptionCitrix Workspace App before 1904 for Windows has Incorrect Access Control. Analysis DescriptionCitrix Workspace App before 1904 for Windows has Incorrect Access Control. SeverityCVSS 3.x Severity and Metrics: NIST:NVD Vector:NVD Vector: | |
| Hyperlink | Resource |
|---|---|
| https://support.citrix.com/article/CTX251986 | Vendor Advisory |
| https://support.citrix.com/v1/search?searchQuery=%22%22&lang=en&sort=cr_date_desc&prod=&pver=&ct=Security+Bulletin | Vendor Advisory |
- Citrix 4.1 Download
- Citrix Workspace 1904 Download
- Citrix Workspace 1904 Download
- Citrix Workspace 1904
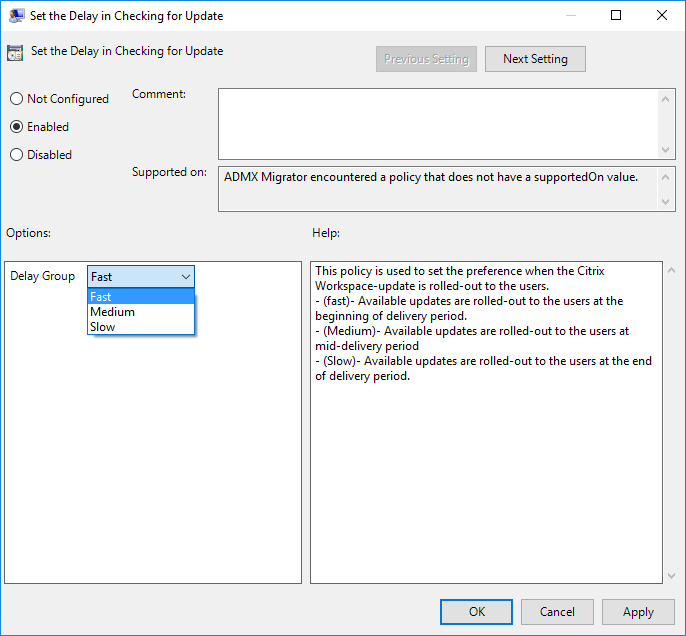
Citrix provides sample scripts that can be downloaded from one of the Workspace app or Receiver download pages (Workspace app version 2103.1 (Current Release), or Workspace app version 1912 CU3 (aka ) (LTSR), Receiver version 4.9.9002 (LTSR) by expanding Downloads for Admins (Deployment Tools). The Citrix Workspace app allows for secure, unified access to all of your SaaS apps, web apps, virtual apps, files, and desktops. If your company uses Citrix, simply login with your company credentials to access all of the resources you need to be productive from anywhere.
How to mass deploy WorkSpace 1904.1 So we’ve got this vulnerability that is patched in WorkSpace 1904.1. My Org has always just popped on the version of receiver or WorkSpace etc. That was current when the image was built.
Weakness Enumeration
| CWE-ID | CWE Name | Source |
|---|---|---|
| NVD-CWE-noinfo | Insufficient Information | NIST |
Known Affected Software Configurations Switch to CPE 2.2
Denotes Vulnerable Software
Are we missing a CPE here? Please let us know.
Iobit driver booster free.
Change History
2 change records found show changesQuick Info
CVE Dictionary Entry:CVE-2019-11634
NVD Published Date:
05/22/2019
NVD Last Modified:
08/24/2020
Source:
MITRE
At least one of these is required:
 TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (0xc030)
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (0xc030)
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (0xc028)
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (0xc013)
Objective
Citrix 4.1 Download
This feature is an important change to the secure communication protocol. Cipher suites with the prefix TLS_RSA_ do not offer forward secrecy and are considered weak. These cipher suites were deprecated in Citrix Receiver version 13.10 with an option for backward compatibility.In this release, the TLS_RSA_ cipher suites have been removed entirely. Instead, this release supports the advanced TLS_ECDHE_RSA_ cipher suites. If your environment is not configured with the TLS_ECDHE_RSA_ cipher suites, client launches are not supported due to weak ciphers.
This document aims to detail the changes to the cipher suites.
What’s New?
The following advanced cipher suites are supported:
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (0xc030)
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (0xc028)
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (0xc013)
In earlier releases, the GPO configuration that was available under the below Computer Configuration node which allowed to enable the deprecated cipher suites has been removed now.
Administrative Template > Citrix Component > Citrix Workspace > Network Routing > Deprecated Cipher Suites
The following cipher matrix provides the ciphers supported by the latest SSL SDK:
Expected failure scenarios and edge cases
TCP My mac store. New app store download.
OPEN mode: Session launch is not supported when the client is configured for GOV and the VDA for COM. This happens because a common cipher suite is absent.
- FIPS/NIST(SP800-52) compliance mode: Session launch is not supported when the VDA is configured for COM the client for COM, GOV, or ANY, or the other way around. This happens because a common cipher suite is absent.
- DTLS v1.0 supports the following cipher suites:
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
- TLS_EMPTY_RENEGOTIATION_INFO_SCSV
- DTLS v1.2 supports the following cipher suites:
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
- TLS_EMPTY_RENEGOTIATION_INFO_SCSV
- Therefore, session launch is not supported from a client configured for GOV to a VDA configured for COM. Also, fallback to TCP is not supported. When you use DTLS v1.0, session launch is not supported for clients configured for GOV because a common cipher suite is absent.
- DTLS does not support FIPS/NIST compliance modes.
- DTLS v1.2 is supported by Windows 10 (1607 and later) and Windows 2016 VDAs. For more information, see Knowledge Center article https://support.citrix.com/article/CTX230010.
- DTLS v1.2 is not supported by Citrix Gateway. This scenario can be tested only with DTLS v1.0. For Citrix Gateway ciphers troubleshooting, see Knowledge Center article https://support.citrix.com/article/CTX235509.
The following matrices provide details of internal and external network connections:
Citrix Workspace 1904 Download
- Matrix for internal network connections (Citrix Gateway scenario)
- Matrix for external network connections (Citrix Gateway scenario)
Citrix Workspace 1904 Download
Citrix Workspace 1904
Note: When NetScaler Gateway is used

- For the EDT to work, NetScaler Gateway must be of version 12.1 or higher since the older versions doesn't support ECDHE cipher suites in DTLS mode.
- NetScaler Gateway doesn't support DTLS 1.2 so TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 and TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 are not supported and NetScaler Gateway must be configured to use TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA for it to work in DTLS 1.0
